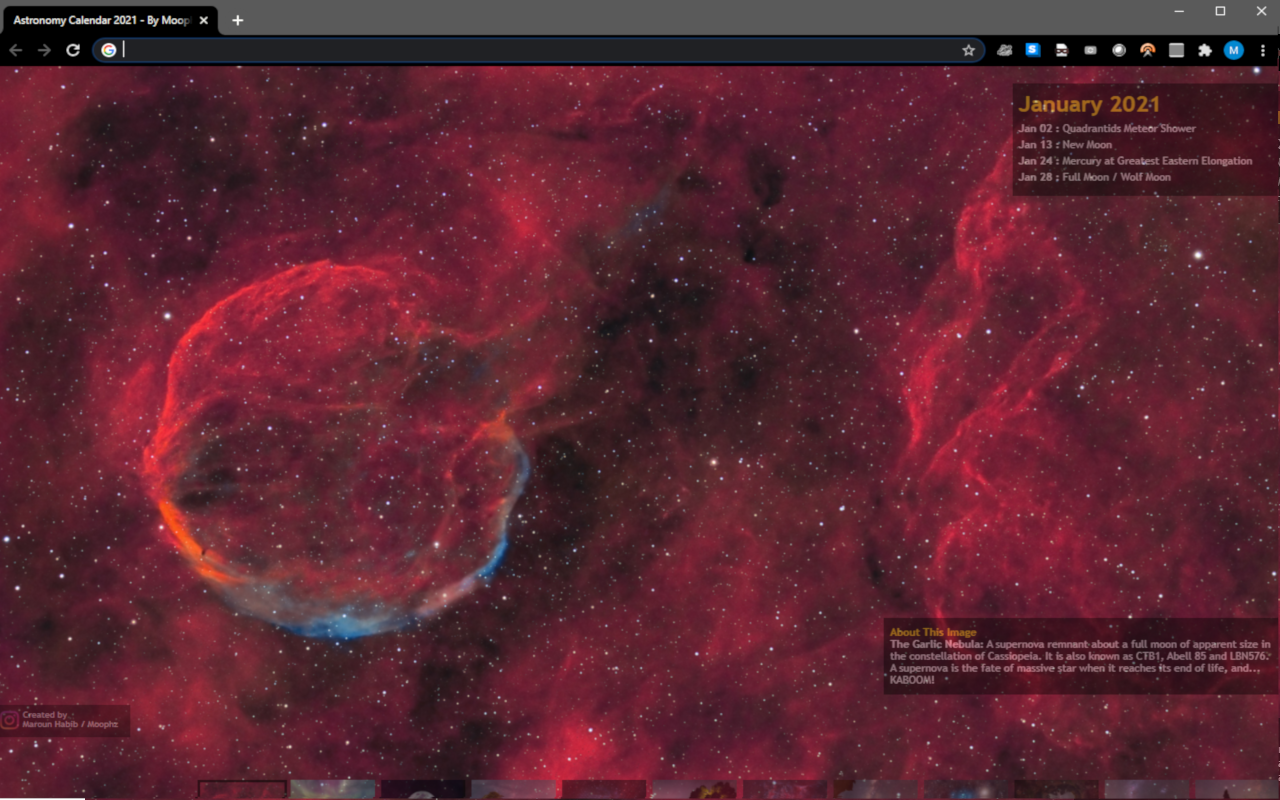
Astronomy Calendar of Celestial events 2021 has gone digital, and you can access it from your favorite browser. It is currently supported for Google Chrome, Mozilla Firefox, Microsoft Edge and others.

Astrophotography in Lebanon during Lockdown
Indoor hobbies have boomed during lockdown, and Deep Sky Astrophotography was no exception.

Astrophotography in some Deserts of the Arab World
The next dark-sky destination is every nightscaper's daydream, and while many go-to locations have been standardized for this matter, breaking out from comfort zones of the well-known ones enables new experiences as an astro-traveler versus an astro-tourist.

La Nuit des Etoiles - Lebanon, August 3rd 2019
Behind Cedar Trees, lies an epic story of resilience and resistance, dating back to biblical times when dense forests covered this land. They are stargazers by nature - always looking up.

Astronomy Calendar - 2019
After putting a tedious effort in what I love the most, rounding edges and carefully nitpicking, I am overly pleased to announce to you that my Astronomy calendar for the y

Astroimagin Together - Lebanese Astrophotographers gathering
It’s safe to say that astrophotography and amateur astronomy has been blooming in Lebanon. On every new moon, astrophotographers relocate their heavy artillery to dark spots for a recurrent date with the stars.

Lebanon celebrates Astronomy Day with USJ Astronomy Club
Lebanon celebrated Astronomy Day. Hundreds of people interested in Astronomy participated from across the country to participate and enjoy the show. The event was of utmost success and raised the bar for future science events in the area.
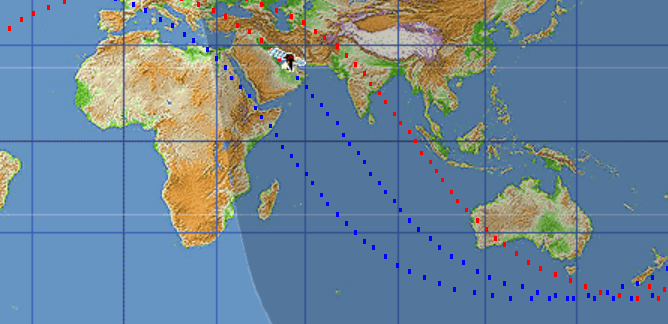
The meteor that allegedly appeared over Dubai is not a meteor
… spoiler alert: not even a UFO. A spectacular bright flying object dashed slowly for 50 seconds through Dubai's sky was spotted and recorded on video. People reportedly thought it was an aircraft crashing, a UFO and even a meteor (some thought that the Russians are invading).
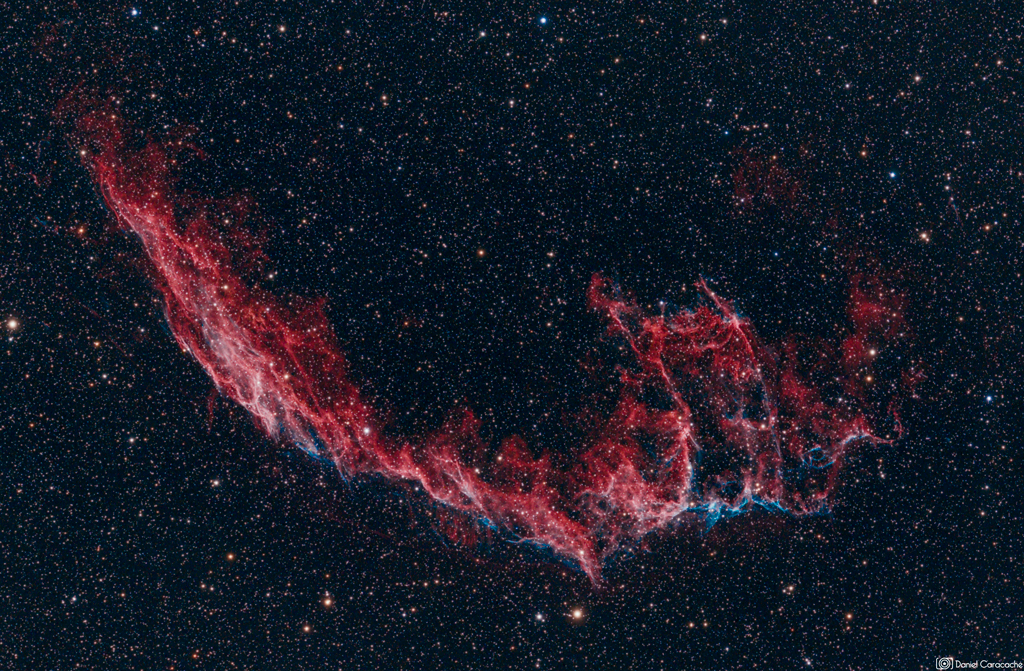
Deep Sky Images from Lebanon, taken by Daniel Caracache
From Lebanon's dark skies with love. Catch the glimpse of Daniel Caracache's flabbergasting Deep Sky Images.

The Milky Way season in Lebanon officially kicked-off for summer 2017
The Milky Way season kicked-off prematurely this year; astrophotographers planned late night trips at 4:30AM after its rise and just a few minutes before sunrise.
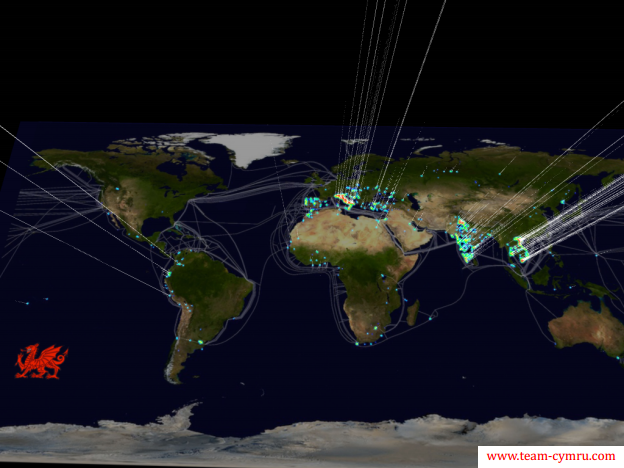
There are no such things as free VPNs and not all VPNs are private
VPNs are pursued by privacy-seekers to circumvent surveillance, but not all VPNs are created equal and few of them are private. As an example, "Onavo Protect" is a Free, popular and a very handy VPN, no privacy seeker is advised to use it because it leaks some data and enables tracking.

Webmasters! Time to enforce HTTPS, no more excuses
If you run or own a website that doesn't enforce HTTPS, browsers will soon flag it as 'Not secure' (simply because it isn't). It's time to enforce HTTPS.

Fraudulent e-shops from Black Friday are still there for your holidays shopping
Many online shoppers purchased from online stores ended up giving away their money to websites that turned out being either fraudulent or non-existing.

ForwardLB - Bridging the gap between Freelancers and Entrepreneurs
A group of enthusiastic techies from Beirut recently launched a not-for-profit co-working hub and startup studio, that aims to build a community of freelancers, independent workers, entrepreneurs and startup teams.
Why Cyber Security Awareness is so important?
Because we don't know what we don't know. Because if things are working doesn't mean they are working securely. Because if things are working securely doesn't mean they will always work securely.

Password Manager - Friend or Foe?
We are living the post-password era. All those accounts we daily create, enclose us between a password that is 'easy' to remember and hard to 'guess'.

Hacking - back to the roots
Hacking is the art and skill of reverse engineering, re-engineering, creating, patching, modding and upgrading things into a more useful state.
From Lebanon to Iceland, Aurora Borealis timelapse
Originally posted on StepFeed: "A Lebanese amateur photographer, who goes by the moniker Moophz, has just released a time-lapse video compilation that he had shot between Lebanon and Iceland."

He sang ER-hamna and you won't believe what happened next!!
Mr. Robot and the odd 218.108.149.373 IP Address

Total Lunar Eclipse - 27/09/2015
Photo of the Total Lunar Eclipse taken from the Cedars of Chouf in Lebanon on the 27th of September 2015.

Ingress, of Megalomania and Social Experiment
Put some good people in a lab (here Niantic Labs), split them into competing teams, give them incrementing powers, make them feel they earn it, watch those 'Good' people turn 'Evil' and how they start abusing their powers against each other in a sadistic manner.
[Timelapse] I have seen the northern lights and here is my timelapse compilation

98.7% Solar Eclipse from Iceland - 20/3/2015
We encountered another twilight this morning after our first Aurora hunting overnight, we returned back to our hotel to recharge our batteries and inject some blood in our caffeine systems, just before shooting a 98.7% Solar Eclipse.

[video] Airplane take off from Beirut, engine failure due to bird strike
36 seconds after takeoff we were already above the sea, we heard the sound of two brutal explosions from the engine underneath, the aircraft started shaking and vibrating, it also smelled burning from the inside. The situation escalated quickly when the "EXIT" signs lit.

Nassim Haramein - Quantum bullshit
How to secure your nude photos?
Deliver yourself from yourself

24 common bloggers mistakes with fixes
Would 2014 be another dark year for cybernauts?
Due to the solemnity of the recently discovered security loopholes (stated subsequently), 2014 is nominated to be the year of credential theft, online payment fraud and privacy violation.
Wrapping up all 2013 DailyZouwedet - #DailyZouwedeh زَوّادَة اليَومِ

17 tips you should know before dating a Hacker
People don't ship with user manuals, whether you dated on purpose or by mistake the `security gal` or `security guy` this will guide you through the do's and don'ts to tweak and maintain a sustainable relationship, full of joy and all those shits.

November 3 2013 - Partial Solar Eclipse seen from Lebanon
Today featured a partial solar eclipse and here are my shots.
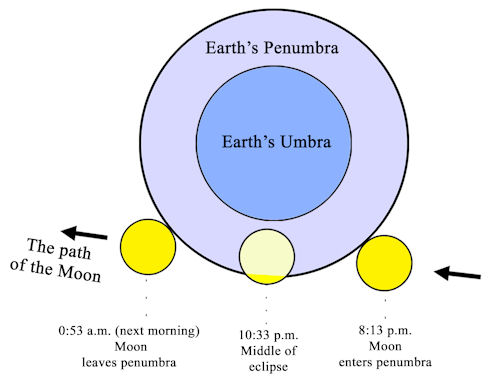
October 18-19 2013 - Penumbral lunar eclipse seen from Lebanon
Yesterday's moon underwent a Penumbral Eclipse, this happens when the moon passes through the earth's penumbra (earth's secondary shadow). Seen from earth, the moon's dish showed subtle changes and got gradually darker from one side.
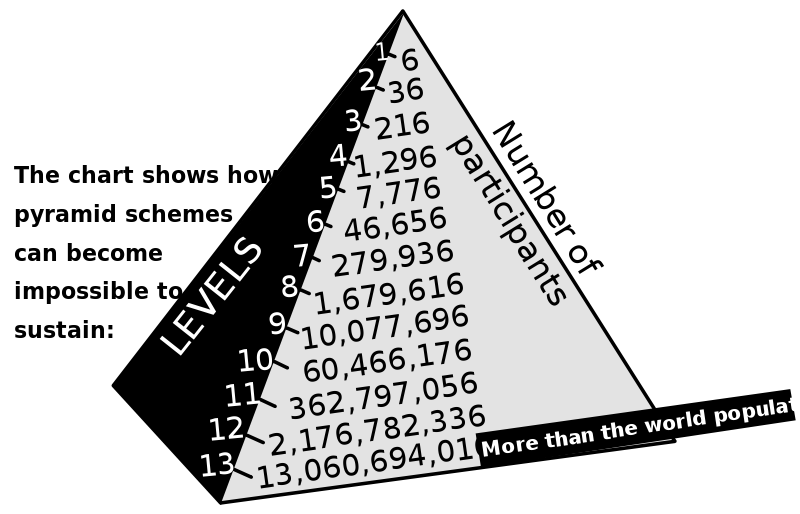
Bonofa Cube7 - Scam your Friends or die trying
Bonopha/Kyoob7 is a pyramid scheme. This post summarises my prematurely-ended drama with them.
Man in the middle attack detection & prevention scripts
In case you are familiar with Man in the middle attacks I don't expect you doing any of those stuff under untrusted WiFi (same for wired ones), else you should think twice before executing any activity under public access points.
Scared? Well you should be !
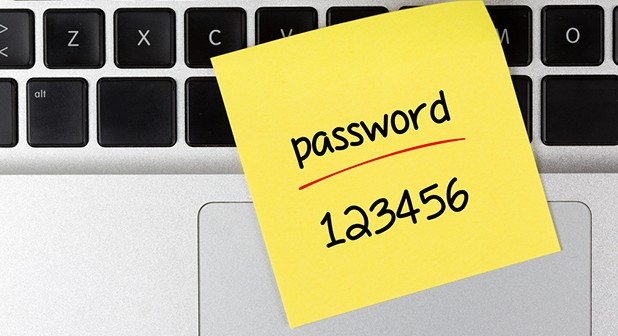
Password Managers - The time is now!
You daily deal with a limited number of passwords you easily memorize despite their complexity. But how about the other numerous ones you don't utilize on daily basis?

Prison break your Comfort Zone
With time, we unintentionally collect several habits that end up being a trap conjoint, yet opposed with comfort. Some of those collections manage to slide into our unconsciousness to define our behavior and thoughts.
Mozart Symphony No.40 - versions, rearrangements and remixes
Below is a list of the versions and interpretations for Mozart's Symphony#40 collected through the years.
Gauss the malware - An electromagnetic cyber espionage tool
Gauss White, a malware hitting targeting the Lebanese Banking Sector; A Nation-state cyber-espionage Trojan, cousin of Flame and Stuxnet. Everything you need to know from a political perspective.

State of Apathy
The last few weeks have seen what can be considered the worst period in Lebanon’s post-war era. It seems as though all of the country’s institutions have broken down altogether; from electricity to security, few characteristics of what makes a land a country can be observed currently more than ever. What is causing this chaos? And how can it be solved?

Stuxnet - Olympic Games Changing its Roots!
According to history books, the Olympic Games has Greek roots and is considered as the world's foremost sports competition.
According to the United States' administration, the Olympic Games has American roots and is considered as the US’s first cyber-attack program.
What is “Olympic Games” and how its root became American?

Blasphemy Freedom of expression?
Imagine how some cultural and beliefs systems, having no relation with logic, intellectuality and realism, are affecting on different aspects of life.

How to survive a Geeky, workaholic, professional IT life?
What good will it be if you gained the source code of the world and yet lost your very self?

[Hacking For Dummies] Breaking into iPhone SMS Database
This document is about hacking and exploiting iPhone vulnerbilities in order to extract the iPhone user's SMS database. You do not need to be a Hacking Guru, many times you can rely on other people's stupidity and bad configurations in order to achieve your goals.

Nadine Mazloum - Citizens of the World Against Belo Monte
Lebanese independent video journalist, Nadine Mazloum has recently released an online environmental video petition entitled: "Citizens of the World Against Belo Monte".

Sperm Data Storage (SDS) - A new way to expand your storage space
How can we not use Sperms for computerized data storage? How can we not profit from space provided by sperm for DNA and replace it by computerized digital data?

The Dilemma
Politics is a word often met with disgust or distrust in Lebanon; it reminds the vast majority of the Lebanese population of the misery they live in.